Why Secure Remote Access Matters for Offshore Hiring
 13 min read
13 min read

Secure remote access is critical for offshore hiring. Without it, businesses face risks like data breaches, compliance violations, and reduced productivity. In 2026, 79% of organizations reported data breaches tied to remote work vulnerabilities, while global cybercrime costs are projected to hit $10.5 trillion annually by 2025. For small businesses, the stakes are even higher – 60% shut down within six months of a breach.
Key takeaways:
- Data protection: Tools like Zero-Trust, MFA, and Secure Web Gateways safeguard sensitive information.
- Improved collaboration: Secure systems enable offshore teams to work efficiently across time zones.
- Trust and accountability: Clear security protocols build confidence between companies and offshore teams.
Talently integrates these solutions at every stage, from talent vetting to payroll, ensuring offshore teams operate securely and efficiently. Investing in secure access isn’t just about avoiding risks – it’s about enabling smooth, reliable global operations.
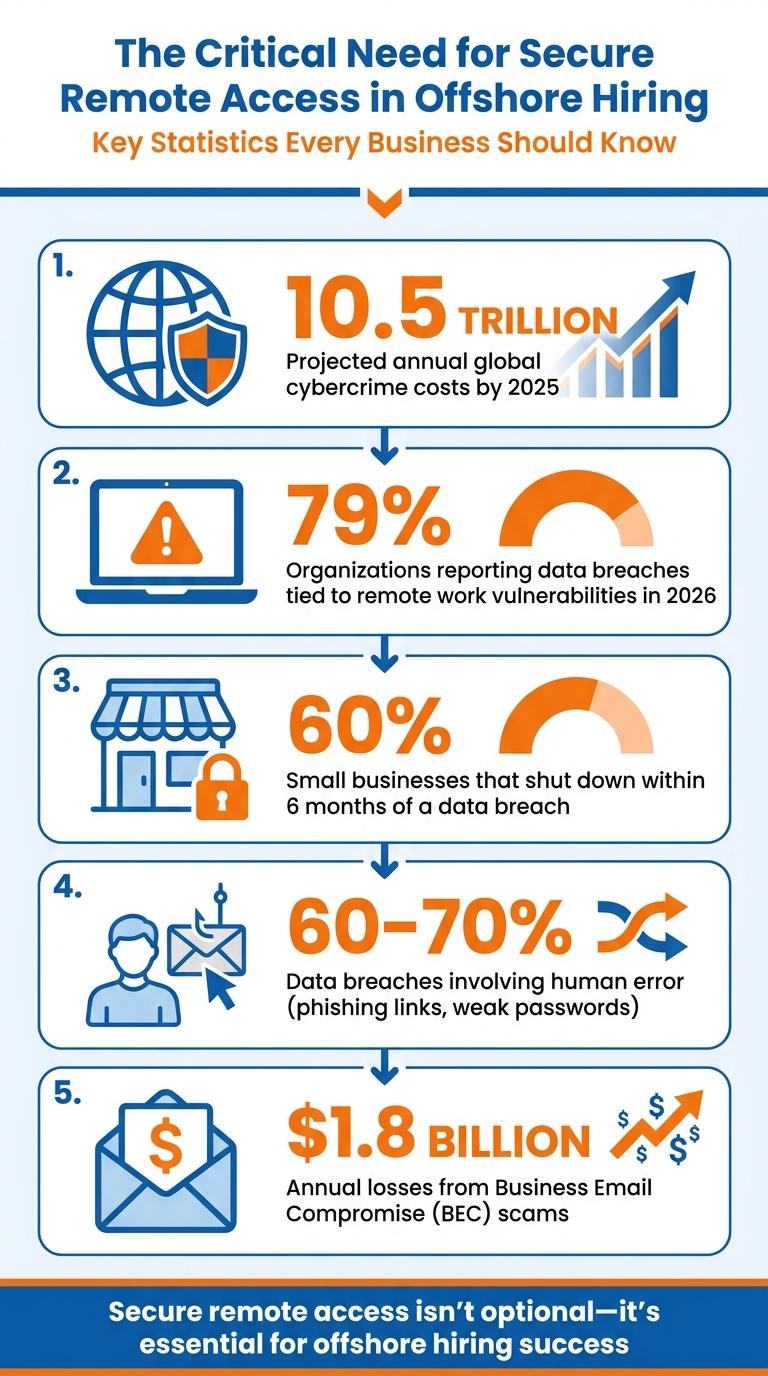
Secure Remote Access Statistics: Cybercrime Costs and Data Breach Impact 2025-2026
Problems When Offshore Hiring Lacks Secure Remote Access
Without proper security measures, offshore hiring can open the door to risks that threaten financial stability, legal compliance, and team relationships.
Data Breaches and Compliance Violations
Inadequate security leaves offshore teams vulnerable to cyberattacks. For example, shared credentials or overly broad access permissions mean a single compromised password can jeopardize multiple systems. Similarly, personal devices lacking encryption, updated antivirus software, or firewalls provide easy entry points for hackers.
The legal stakes are equally high. Failing to implement secure access protocols can lead to violations of regulations like GDPR, CCPA, HIPAA, or PCI-DSS, especially if sensitive data is processed in unauthorized regions. The Ponemon Institute highlights the gravity of this issue:
"The necessity for robust data protection measures is underscored by the fact that 60% of small businesses go out of business within six months of a data breach."
Human error plays a significant role in these breaches, with 60% to 70% involving actions like clicking phishing links or using weak passwords. Business Email Compromise (BEC) scams alone caused $1.8 billion in losses in a single year.
Beyond the legal and financial fallout, these breaches disrupt daily operations and create lasting challenges for teams.
Lower Productivity and Collaboration Problems
Security gaps don’t just invite breaches – they also disrupt teamwork. Without secure, easy-to-use tools, offshore teams may turn to unauthorized apps like personal messaging platforms or unapproved cloud storage. This leads to fragmented data, information silos, and version control headaches, making it harder to keep track of critical files and processes.
Additionally, without centralized logging or clear escalation procedures, addressing security incidents becomes slower and costlier. Downtime caused by these issues can cripple productivity, especially when compounded by managing remote teams across time zones and limited IT support on-site. In crisis situations, the lack of secure communication channels only makes matters worse, hindering effective resolution.
Loss of Trust in Offshore Employees
Lastly, poor security measures erode trust between companies and their offshore teams. Without secure access and monitoring tools, businesses lack visibility into daily workflows. This lack of transparency can lead to suspicion and anxiety, damaging morale and making it harder for offshore employees to feel like part of the team.
Unmanaged personal devices add another layer of risk, fueling concerns about data leaks and unauthorized access. When companies can’t distinguish between accidental mistakes and intentional misconduct due to the absence of auditable logs, trust within the team takes a hit.
These challenges – breaches, operational disruptions, and diminished trust – don’t just harm business integrity; they also weaken the relationships and cohesion that are essential for success in offshore hiring. Without clear security protocols, any uncertainty around data handling can lead to vulnerabilities that undermine both team dynamics and overall business goals.
sbb-itb-7512dae
Why Secure Remote Access Matters for Offshore Hiring
Proper remote access protocols can turn offshore hiring into a game-changer for North American companies collaborating with South African professionals. These protocols ensure smooth teamwork, safeguard sensitive data, and create well-integrated teams. Let’s dive into how they achieve these outcomes.
Supporting Cross-Time-Zone Collaboration
Secure remote access ensures work continues seamlessly despite the time differences between the U.S. East Coast and South Africa. For instance, when offshore employees encounter system failures or IT issues, secure systems allow them to resume work independently – even if North American security teams are offline. Automated security updates further ensure offshore teams stay productive without waiting for manual interventions.
Tools like Zero-Trust Network Access (ZTNA) provide a more secure alternative to traditional VPNs, creating a unified security framework for both onshore and offshore teams. Additionally, secure video conferencing and encrypted messaging platforms support real-time communication during overlapping work hours, speeding up task transitions and cutting down on delays.
Protecting Confidential Business Data
Modern security frameworks focus less on the location of employees and more on how they access company systems. Zero-Trust Architecture and Role-Based Access Control (RBAC) verify every access attempt, ensuring offshore staff only reach the data they need, which significantly lowers the risk of breaches. Geographic data controls and Virtual Desktop Infrastructure (VDI) further centralize sensitive information, keeping it compliant with regulations.
For tasks requiring extra security, VDI ensures critical data stays on centralized servers rather than being stored locally on offshore devices. Combined with endpoint security measures like Mobile Device Management (MDM), companies can remotely erase data from lost or stolen devices, adding an extra layer of protection for sensitive information.
Improving Offshore Team Integration
Strong security protocols aren’t just about protection – they also foster trust and streamline operations. By providing encrypted, company-owned hardware and implementing precise RBAC, companies can reduce onboarding challenges and promote team cohesion. Secure remote access also reassures clients and stakeholders that sensitive data is tightly controlled, which can be a key factor in securing contracts.
How to Implement Secure Remote Access for Offshore Teams
Securing remote access for offshore teams requires a layered approach. By using the right mix of modern tools, you can protect sensitive data while maintaining smooth workflows.
Zero-Trust Network Access (ZTNA)
ZTNA shifts away from the outdated "trust but verify" model to one of constant verification at every access point. Instead of granting offshore employees full network access via a VPN, ZTNA provides application-specific permissions based on job roles. For instance, a graphic designer might only access design tools and shared folders – nothing beyond that.
To implement ZTNA effectively, follow a 90-day plan:
- Inventory access points and identify risks.
- Enforce controlled access and address endpoint vulnerabilities.
- Test and recertify controls quarterly, assigning internal owners to maintain consistency.
Stolen credentials played a role in 22% of confirmed breaches in 2025, a risk that grows when offshore teams access systems across time zones. Additionally, third-party pathways were linked to 30% of incidents. ZTNA helps mitigate these risks through micro-segmentation, which limits the damage attackers can do if one account is compromised. For example, closing port 3389 and routing remote desktop access through ZTNA can prevent attackers from exploiting Remote Desktop Protocol (RDP) vulnerabilities.
Once application-specific access is secured, adding MFA and endpoint security enhances protection even further.
Multi-Factor Authentication (MFA) and Endpoint Security
MFA strengthens security by requiring multiple forms of verification, such as a device or biometric check, in addition to a password. However, not all MFA methods are equally secure. Phishing-resistant MFA, like FIDO2 hardware security keys, should be used for high-risk accounts, such as IT administrators or finance staff. SMS- and push-based MFA can be vulnerable to attacks like MFA fatigue. On average, MFA costs between $3 and $9 per user each month.
Endpoint security ensures that devices meet health standards – checking for updated operating systems, encryption, and active endpoint detection and response (EDR) tools – before granting access. For instance, if an offshore worker’s laptop has outdated antivirus software, access is blocked until the issue is fixed. This service typically costs $4–$12 per device per month.
"Remote-work security is not a VPN feature. It is a repeatable operating model that combines identity policy, endpoint trust, secure access pathways, and governance discipline." – Nandor Katai, Valydex
To further protect against vulnerabilities, automate patching for internet-facing systems within a few days of disclosure. Exploits often occur within 9 to 13 days of vulnerability announcements. Since phishing click rates for untrained employees hover around 32% to 34%, endpoint protection becomes a critical safeguard for offshore teams.
With identities and devices secured, the next step is filtering web traffic through secure gateways.
Secure Web Gateways (SWG) as VPN Alternatives
SWGs inspect and filter web traffic via a cloud-based platform, blocking malicious content before it reaches offshore devices. Unlike traditional VPNs, which extend an entire corporate network to remote users, SWGs enforce security policies at the application and URL level. This is crucial because 91% of security leaders worry about VPN-related breaches, and 56% of organizations have already experienced at least one VPN-related cyberattack.
SWGs are part of the Secure Access Service Edge (SASE) framework, which combines network and security functions into a single, cloud-native service. This eliminates the need for hardware appliances, making it easier to scale for global teams. Choose an SWG capable of inspecting encrypted HTTPS traffic to prevent malware from bypassing security measures. For offshore teams using SaaS platforms like Microsoft 365 or Salesforce, SWGs secure direct cloud connections without the latency issues associated with VPNs.
"With so many users off the network and so many applications in the cloud, does it even make sense to connect remote users to the internal network?" – Zscaler
Transitioning from VPNs to SWG/SASE not only reduces latency but also keeps internal resources hidden from unauthorized users. With zero-day exploits targeting edge devices and VPNs increasing nearly eightfold in the past year, cloud-based solutions are becoming essential for secure offshore operations.
How Talently Provides Secure Remote Access for Offshore Staffing
When North American companies hire South African professionals through Talently, security is at the core of every step. From interviews to payroll, Talently integrates enterprise-level protocols to safeguard sensitive information while ensuring smooth collaboration across time zones. These security measures are woven into every stage of the offshore hiring process, creating a reliable framework for global operations.
Security Protocols in Talent Sourcing and Vetting
Talently employs AI-driven interviews tailored to specific roles – whether in customer success, marketing, or software development. This technology helps objectively screen candidates and minimize insider risks.
"Talently.ai efficiently assesses technical and non-technical skills and filters out unqualified applicants without any biases." – Talently.ai
By restricting access to only pre-vetted, high-performing professionals, Talently addresses potential security threats right from the start. Considering that 82% of organizations identify data and cybersecurity risks as major concerns when hiring offshore, this initial layer of security is critical.
Secure Compliance and Payroll Management
Talently ensures compliance with South African labor laws, including the BCEA and LRA, embedding remote work and data protection clauses into employment contracts.
The platform also handles statutory contributions like PAYE, UIF, and SDL, aligning payroll processes with local regulations while meeting North American security standards. To further protect financial transactions, Talently incorporates SOC 2–aligned contracts and cyber-liability coverage, often up to $3 million.
"Security compliance is now a baseline expectation for third‑party and offshore partners." – Insight Global
Technology for Secure Team Collaboration
Secure collaboration tools are just as essential as compliance and vetting. Talently ensures real-time collaboration for roles like customer success, graphic design, and marketing by setting up secure system access and backup communication channels. This is especially important in South Africa, where load-shedding (planned power outages) can occasionally disrupt connectivity. To counter this, Talently establishes redundant systems and encrypted video conferencing to maintain productivity.
The platform also includes documented IP assignments and NDAs in its onboarding process, alongside strict policies for device and system access. For example, offshore employees in customer success roles receive tailored permissions, granting them access to essential tools like CRM systems without exposing the broader network. With 88% of South African professionals favoring remote or hybrid work setups, Talently’s tech infrastructure supports flexible collaboration while maintaining strict security controls.
Conclusion
Secure remote access lays the groundwork for making offshore hiring both effective and reliable. Without it, the stakes are high – data breaches can cost up to $10.5 trillion annually, and 60% of small businesses fail within six months of a breach. Implementing robust security frameworks ensures offshore teams are just as secure as in-house staff, shifting the focus from physical location to secure data access.
The key lies in combining Zero-Trust Architecture, Multi-Factor Authentication, and role-based access controls. These measures protect sensitive data, enable real-time collaboration across time zones, and replace physical oversight with documented accountability. This approach builds genuine trust between North American companies and their offshore teams.
By adopting these systems, businesses not only reduce risks but also improve efficiency. Talently integrates security at every step – covering vetting, compliance, and team collaboration – helping companies cut administrative burdens and save up to 70% on operational costs.
When security becomes a natural part of daily operations, offshore hiring shifts from being a potential risk to a strategic advantage. This seamless blend of security and efficiency turns offshore staffing into a powerful tool for companies competing in the global talent market.
FAQs
What security setup should offshore hires have on day one?
Offshore hires need to adopt Zero-Trust architecture and role-based access controls right from the start. These security measures are essential for protecting sensitive information and ensuring safety, no matter where employees are located. Putting these protocols in place from day one creates a secure remote work setup and shields critical business data effectively.
How do I give offshore staff access without exposing my whole network?
To give offshore staff secure access without putting your entire network at risk, consider adopting a Zero-Trust architecture. This approach ensures that every access request is verified, regardless of where it originates. Pair this with role-based access controls (RBAC) to restrict permissions, granting employees access only to the resources they need for their specific tasks.
To further safeguard your network, use VPNs to establish encrypted connections for all traffic. Together, these strategies help protect sensitive data while allowing your team to work efficiently and securely.
What’s the fastest way to stay compliant with remote offshore work?
To quickly ensure compliance in remote offshore work, it’s crucial to establish a solid security framework. Prioritize Zero-Trust architecture, role-based access controls, and strict access policies. These steps help safeguard sensitive information, secure networks, and actively monitor for potential threats. With these measures in place, you can protect data and stay compliant, regardless of your team’s location.
Related Blog Posts
Ready to build your dream team?
Book a free consultation and get your first candidate shortlist within 48 hours.
No upfront fee • Only pay if you hire
